Hi guys,
I’m trying to implement SSO for a web application (node.js) w/ two factor authentication (U2F tokens), so privacyIDEA was decided upon to handle the token part while SimpleSAMLphp would be configured as an Identity Provider and finally a package like passport-saml to act as a bridge between SimpleSAMLphp and the web application utilising SAML protocol to manage such communication process.
Now, I’ve followed this guide to install privacyIdEA and SimpleSAMLphp on the same server, and here are the Apache configuration files for each - I’m using self signed certificates btw.
privacyIDEA
<VirtualHost *:443>
ServerAdmin webmaster@localhost
# You might want to change this
ServerName pi.is.com
DocumentRoot /var/www
<Directory />
# For Apache 2.4 you need to set this:
Require all granted
Options FollowSymLinks
AllowOverride None
</Directory>
# Yubico servers use /wsapi/2.0/verify as the path in the
# validation URL. Some tools (e.g. Kolab 2fa) let the
# user/admin change the api host, but not the rest of
# the URL. Uncomment the following two lines to reroute
# the api URL internally to privacyideas /ttype/yubikey.
#RewriteEngine on
#RewriteRule "^/wsapi/2.0/verify" "/ttype/yubikey" [PT]
# We can run several instances on different paths with different configurations
WSGIScriptAlias / /etc/privacyidea/privacyideaapp.wsgi
#WSGIScriptAlias /instance1 /home/cornelius/src/privacyidea/deploy/privacyideaapp1.wsgi
#WSGIScriptAlias /instance2 /home/cornelius/src/privacyidea/deploy/privacyideaapp2.wsgi
#WSGIScriptAlias /instance3 /home/cornelius/src/privacyidea/deploy/privacyideaapp3.wsgi
#
# The daemon is running as user 'privacyidea'
# This user should have access to the encKey database encryption file
WSGIDaemonProcess privacyidea processes=1 threads=15 display-name=%{GROUP} user=privacyidea
WSGIProcessGroup privacyidea
WSGIPassAuthorization On
ErrorLog /var/log/apache2/error.log
LogLevel warn
# Do not use %q! This will reveal all parameters, including setting PINs and Keys!
# Using SSL_CLINET_S_DN_CN will show you, which administrator did what task
LogFormat "%h %l %u %t %>s \"%m %U %H\" %b \"%{Referer}i\" \"%{User-agent}i\"" privacyIDEA
CustomLog /var/log/apache2/ssl_access.log privacyIDEA
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
SSLProtocol ALL -SSLv2 -SSLv3
SSLHonorCipherOrder On
SSLCipherSuite ECDH+AESGCM:DH+AESGCM:ECDH+AES256:DH+AES256:ECDH+AES128:DH+AES:RSA+AESGCM:RSA+AES:!aNULL:!MD5:!DSS
# If both key and certificate are stored in the same file, only the
# SSLCertificateFile directive is needed.
SSLCertificateFile /etc/ssl/certs/privacyideaserver.pem
SSLCertificateKeyFile /etc/ssl/private/privacyideaserver.key
<FilesMatch "\.(cgi|shtml|phtml|php)$">
SSLOptions +StdEnvVars
</FilesMatch>
<Directory /usr/lib/cgi-bin>
SSLOptions +StdEnvVars
</Directory>
BrowserMatch ".*MSIE.*" \
nokeepalive ssl-unclean-shutdown \
downgrade-1.0 force-response-1.0
</VirtualHost>
# If you want to forward http request to https enable the
# following virtual host.
<VirtualHost _default_:80>
# # This will enable the Rewrite capabilities
RewriteEngine On
#
# # This checks to make sure the connection is not already HTTPS
RewriteCond %{HTTPS} !=on
RewriteRule ^/?(.*) https://%{SERVER_NAME}/$1 [R,L]
</VirtualHost>
# vim: syntax=apache ts=4 sw=4 sts=4 sr noet
SimpleSAMLphp
<VirtualHost *:443>
ServerName idp.sso.com
DocumentRoot /var/www/simplesaml
SetEnv SIMPLESAMLPHP_CONFIG_DIR /var/simplesamlphp/config
Alias /simplesaml /var/simplesamlphp/www
<Directory /var/simplesamlphp/www/>
Require all granted
</Directory>
RedirectMatch ^/$ https://idp.sso.com/simplesaml
SSLEngine on
SSLCertificateFile /etc/apache2/ssl/simplesaml.crt
SSLCertificateKeyFile /etc/apache2/ssl/simplesaml.key
</VirtualHost>
# If you want to forward http request to https enable the
# following virtual host.
<VirtualHost _default_:80>
# # This will enable the Rewrite capabilities
RewriteEngine On
#
# # This checks to make sure the connection is not already HTTPS
RewriteCond %{HTTPS} !=on
RewriteRule ^/?(.*) https://%{SERVER_NAME}/$1 [R,L]
</VirtualHost>
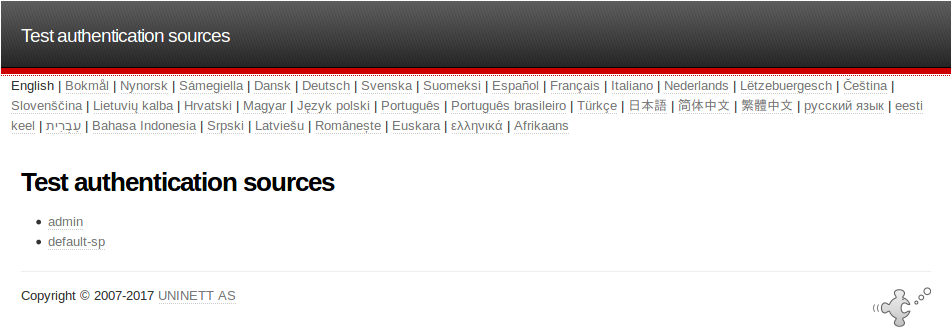
After making sure that both websites run smoothly, and I’m able to login to both, I followed this tutorial, hoping to replace the OTP w/ U2F, but sadly privacyIDEA login doesn’t show up as illustrated down below.
Although, I’ve followed howtoforge’s guide faithfully, yet it seems like the configurations aren’t being read.