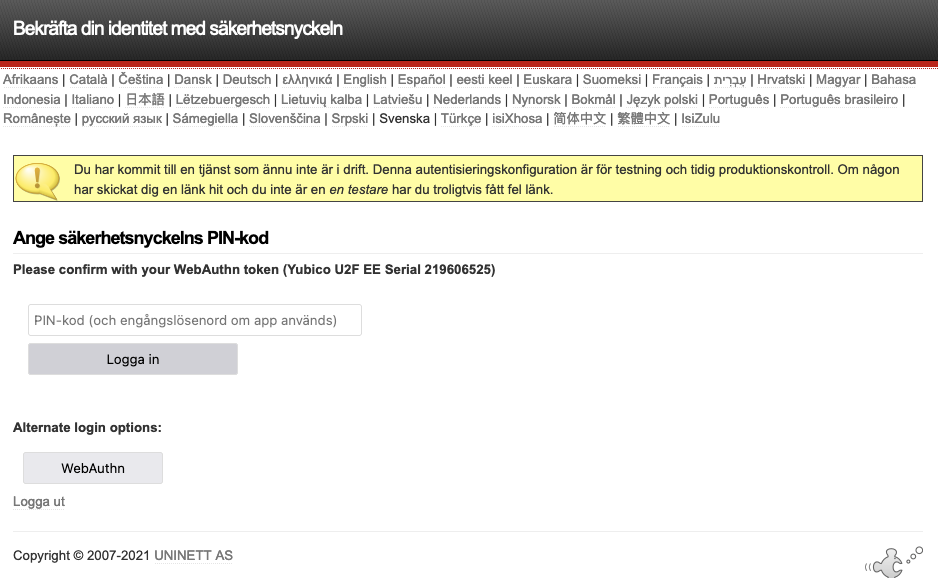
As we need to move from U2F to WebAuthn (still using Yubikeys) I installed the updated Privacyidea-simplesaml-module on our test IdP. Authsource method seems not to work at all while authproc setup does, but will need some tweaking before going to production. The authsource config in authsources.php looks:
‘pi2f’ => array(
‘privacyidea:PrivacyideaAuthSource’,
‘privacyideaserverURL’ => ‘https://2f.skola.engelholm.se:443’,
‘sslverifyhost’ => ‘false’,
‘sslverifypeer’ => ‘false’,
‘realm’ => ‘’,
‘serviceAccount’ => ‘testanv@superadmins’,
‘servicePass’ => ‘***************’,
‘doTriggerChallenge’ => ‘false’,
‘doSendPassword’ => ‘false’,
‘otpFieldHint’ => ‘OTP’,
‘passFieldHint’ => ‘Password’,
‘attributemap’ => array(
‘username’ => ‘cn’,
‘surname’ => ‘sn’,
‘givenname’ => ‘givenName’,
‘email’ => ‘mail’,
),
),
(the service account bit was not particularly well documented, had to guess my way there). When testing the authsource in SSP the message is Error : Unable to reach the authentication server (3)
SSP logs quite a number of errors during this process, most of which means little to me, but this one seems weird:
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 7 [6950280ee4] Form data: username=btw2912, pass=, otp=1234651386, mode=otp, pushAvailable=0, otpAvailable=1, modeChanged=0, webAuthnSignResponse=, webAuthnSignRequest=, origin=, u2fSignRequest=, u2fSignResponse=, message=, loadCounter=1
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 7 [6950280ee4] Server config: privacyideaserverURL=https.skola.engelholm.se, sslverifyhost=false, sslverifypeer=false, realm=, serviceAccount=testanv, servicePass=’’’’’’’’’’’’’’’’’’’’’’’’’’’’, doTriggerChallenge=false, doSendPassword=false, otpFieldHint=OTP, passFieldHint=Password
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 7 [6950280ee4] privacyIDEA: client ip: 10.255.255.39
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] SimpleSAML\Error\Exception: Error 8 - Undefined index: privacyideaServerURL at /var/simplesamlphp/modules/privacyidea/lib/Auth/utils.php:48
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] Backtrace:
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] 5 /var/simplesamlphp/www/_include.php:44 (SimpleSAML_error_handler)
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] 4 /var/simplesamlphp/modules/privacyidea/lib/Auth/utils.php:48 (sspmod_privacyidea_Auth_utils::authenticatePI)
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] 3 /var/simplesamlphp/modules/privacyidea/lib/Auth/Source/AuthSourceLoginHandler.php:56 (sspmod_privacyidea_Auth_Source_AuthSourceLoginHandler::authSourceLogin)
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] 2 /var/simplesamlphp/modules/privacyidea/www/formbuilder.php:72 (require)
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] 1 /var/simplesamlphp/lib/SimpleSAML/Module.php:266 (SimpleSAML\Module::process)
Jan 10 15:25:46 esn-test-idp2 simplesamlphp[874]: 3 [6950280ee4] 0 /var/simplesamlphp/www/module.php:10 (N/A)
Server config: privacyideaserverURL=https.skola.engelholm.se looks wrong to me. However, when using the authproc filter method authentication actually works with TOTP, U2F and WebAuthn even though SSP logs a bunch of errors and lines like the one with the strange PI server URL.
I think the setup here is quite straightforward and “vanilla” so I wonder what I am missing here.
Kind regards
Bengt