I’m using a customized logging.cfg configuration with my PI 3.2 server. After authenticating with AD credentials in ADFS and being prompted to enter PrivacyIDEA MFA token, the authentication attempt does not get logged. The integration works, I can log into the ADFS related service with my MFA token, the attempt just isn’t logged. Digging through the ADFSProvider code on GitHub, it appears to make an http call to the /validate/check endpoint, so I would assume it should show up in the audit log or server log, but it does not. Do I have my logger.cfg configured improperly?
[handlers]
keys=audit
[handler_audit]
class=logging.handlers.RotatingFileHandler
backupCount=7
maxBytes=100000000
formatter=detail
level=INFO
args=('/var/log/privacyidea/audit.log',)
[loggers]
keys=root,audit
[logger_root]
level=NOTSET
handlers=audit
[logger_audit]
handlers=audit
qualname=pi-audit
level=INFO
[formatters]
keys=detail
[formatter_detail]
class=privacyidea.lib.log.SecureFormatter
format=[%(asctime)s][%(levelname)s][%(name)s]%(message)s
The qualname “pi-audit” you specified does not exist.
Your understanding of the log file might be wrong. It does not log a dedicated request like failed authentiction request. I am not sure, if we have such a log message at all.
The log file logs very detailed debug messages and warnings.
So your problem has nothing to do with the ADFS Provider but with the wrong expectations of the log file and wrong config.
You probably want to look at the audit log and filter for “validate/check”, so see that and why the user fails to authenticate.
Oh my understanding is definitely wrong, I don’t understand it at all, lol. I tried to spend some time learning the syntax and everything, but came away with more unanswered questions. The config was provided to me by another user on these forums when I originally asked about logging.
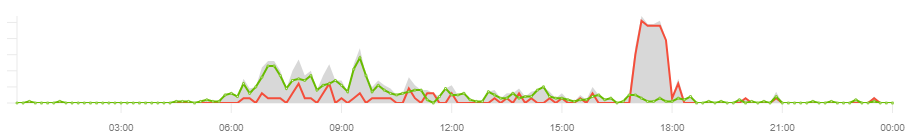
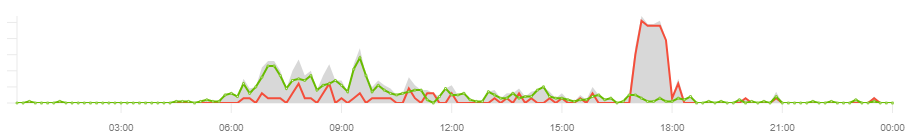
I’m not trying to figure out why a particular user failed to log in. I am exporting specific lines of the log to an Elastic Stack instance that aggregates the data. This way I can identify potentially compromised accounts. This method works great when dealing with RADIUS authentication and we’ve already identified two instances of credential exposure. The below is one such example of identifying a potential credential breach.
However, it appears that PrivacyIDEA-ADFS originating authentications fly under the radar. I tagged you in that issue @cornelinux, hoping to consolidate the discussion somewhere.
The log file is not directly ment to identify single requests.
Take a look here: https://www.privacyidea.org/event-based-logging-with-privacyidea-and-logstash/