(privacyIDEA 3.6.3 on Ubuntu 20.04)
Hi all, I’m a newbie In Privacyidea, but I eventually made up to put all working fine.
On my setup PrivacyIdea is integrated with a freeradius to authenticate Cisco Routers and the Active Directory as IDP. I have a authentication policy that make push tokens to work and an authorization policy that send the privilege level back to the Radius server and then to the Router.
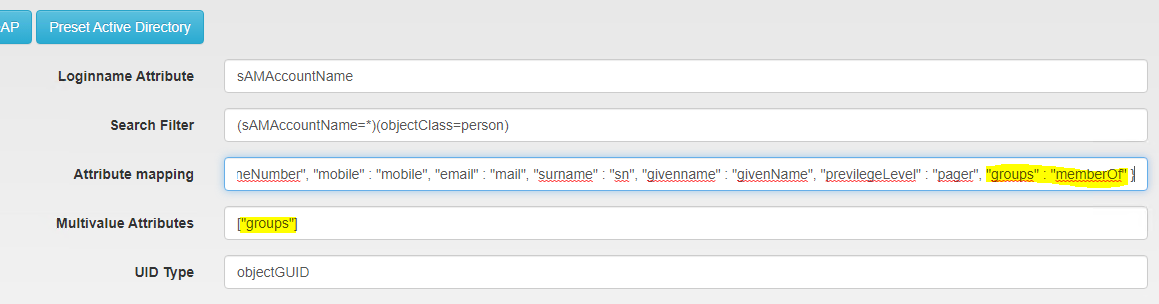
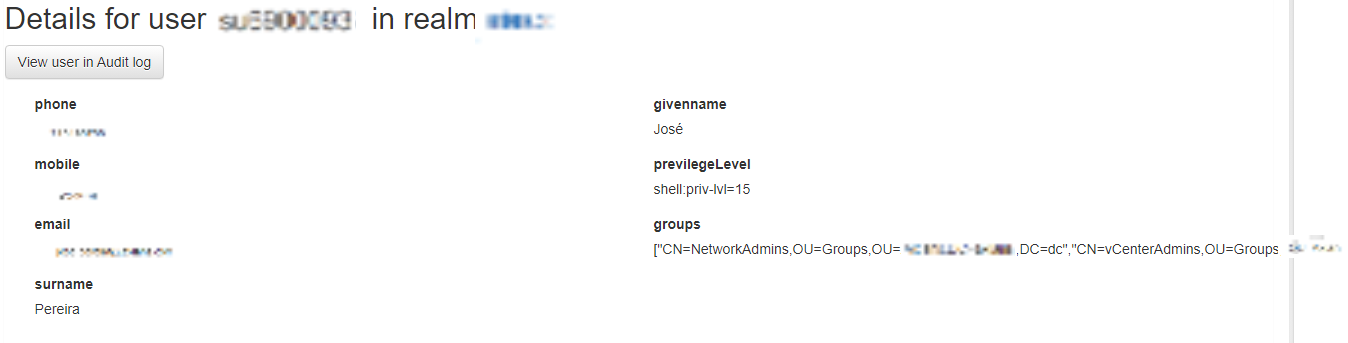
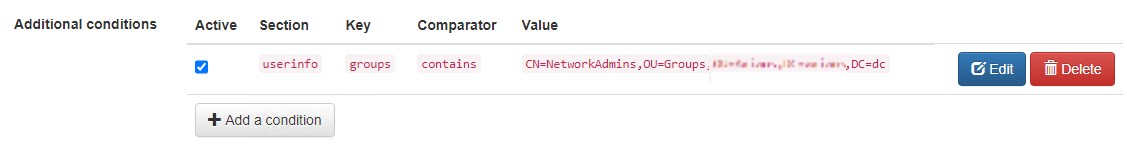
Up to here all is good, now I would like to limit (authentication policy) the access only for users belonging to certain AD groups (memberOf). I’ve follow the PrivacyIdea example in here 7.9. Policy conditions — privacyIDEA 3.6.2 documentation , but for authentication policy instead of webui policy and I can see that PrivacyIdea sees the users belonging to the group but the mach never happens. I’ve also try it to do it to the webui policy, exactly as in the example, but still not working. Is there a matching problem in the Policies Additional Conditions?
I got this when tailing privacyidea.log:
[2022-03-01 11:43:06,477][8012][140403842049792][INFO][privacyidea.lib.user:236] user 'su6900093' found in resolver 'axians.dc'
[2022-03-01 11:43:06,477][8012][140403842049792][INFO][privacyidea.lib.user:238] userid resolved to '2e5e096c-b152-480f-bc9e-665bfd26c292'
[2022-03-01 11:43:06,483][8012][140403842049792][ERROR][privacyidea.lib.policy:922] Policy 'webui' has condition on userinfo, but the according object is not available - possible programming error File "/opt/privacyidea/lib/python3.8/site-packages/flask/app.py", line 2464, in __call__
return self.wsgi_app(environ, start_response)
File "/opt/privacyidea/lib/python3.8/site-packages/flask/app.py", line 2447, in wsgi_app
response = self.full_dispatch_request()
File "/opt/privacyidea/lib/python3.8/site-packages/flask/app.py", line 1950, in full_dispatch_request
rv = self.dispatch_request()
File "/opt/privacyidea/lib/python3.8/site-packages/flask/app.py", line 1936, in dispatch_request
return self.view_functions[rule.endpoint](**req.view_args)
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/api/lib/prepolicy.py", line 154, in policy_wrapper
return wrapped_function(*args, **kwds)
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/api/lib/prepolicy.py", line 154, in policy_wrapper
return wrapped_function(*args, **kwds)
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/api/lib/prepolicy.py", line 154, in policy_wrapper
return wrapped_function(*args, **kwds)
[Previous line repeated 1 more time]
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/api/lib/postpolicy.py", line 109, in policy_wrapper
return self.function(self.request, response, *args, **kwds)
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/api/lib/postpolicy.py", line 526, in get_webui_settings
hide_welcome = Match.generic(g, scope=SCOPE.WEBUI, action=ACTION.HIDE_WELCOME,
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/lib/policy.py", line 2580, in any
return bool(self.policies(write_to_audit_log=write_to_audit_log))
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/lib/policy.py", line 2569, in policies
return self._g.policy_object.match_policies(audit_data=audit_data, request_headers=request_headers,
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/lib/log.py", line 155, in log_wrapper
return func(*args, **kwds)
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/lib/policy.py", line 750, in match_policies
reduced_policies = self.filter_policies_by_conditions(reduced_policies, user_object, request_headers,
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/lib/policy.py", line 785, in filter_policies_by_conditions
if not self._policy_matches_info_condition(policy, key, comparator, value,
File "/opt/privacyidea/lib/python3.8/site-packages/privacyidea/lib/policy.py", line 924, in _policy_matches_info_condition
u"{!s}.".format(policy['name'], type, ''.join(traceback.format_stack()))